Is your organization vulnerable to hidden surveillance threats? This article provides a complete overview of Technical Surveillance Counter Measures (TSCM), offering actionable insights to protect your business from the dangers of industrial espionage and electronic eavesdropping.
Table of Contents
- Understanding the Need for Electronic Bug Sweeps (What are TSCM?)
- Essentials of a Proactive TSCM Strategy
- Understanding Legal and Financial Risks
- Developing a Customised TSCM Plan
- TSCM for Supply Chain Security and Mergers & Acquisitions
- Special Considerations for Government Agencies
- Key Qualities in a TSCM Service Provider
What are Technical Surveillance Counter Measures?
NSI Global provides a range of Technical Surveillance Counter Measures (TSCM) services to help individuals, businesses, organisations and government departments protect against electronic eavesdropping. A TSCM survey, also known as Electronic Bug Sweeps, Security Sweeps, Electronic Bug Detection, or Office Debugging, is a service provided to detect the presence of and report on, hidden technical surveillance devices and hazards. It also identifies technical security weaknesses that attackers could exploit to conduct a technical penetration of the surveyed premises.
Common Eavesdropping Methods and Devices
Covert eavesdropping methods have evolved beyond basic wiretaps to incorporate a range of advanced digital devices. These discreet gadgets possess the capability to intercept wireless signals, record conversations, and harvest digital data. Cleverly concealed within commonplace items, these devices present a formidable challenge for detection. It is imperative to grasp the intricacies of these sophisticated methods and the electronic devices employed to bolster protection against unauthorized surveillance.
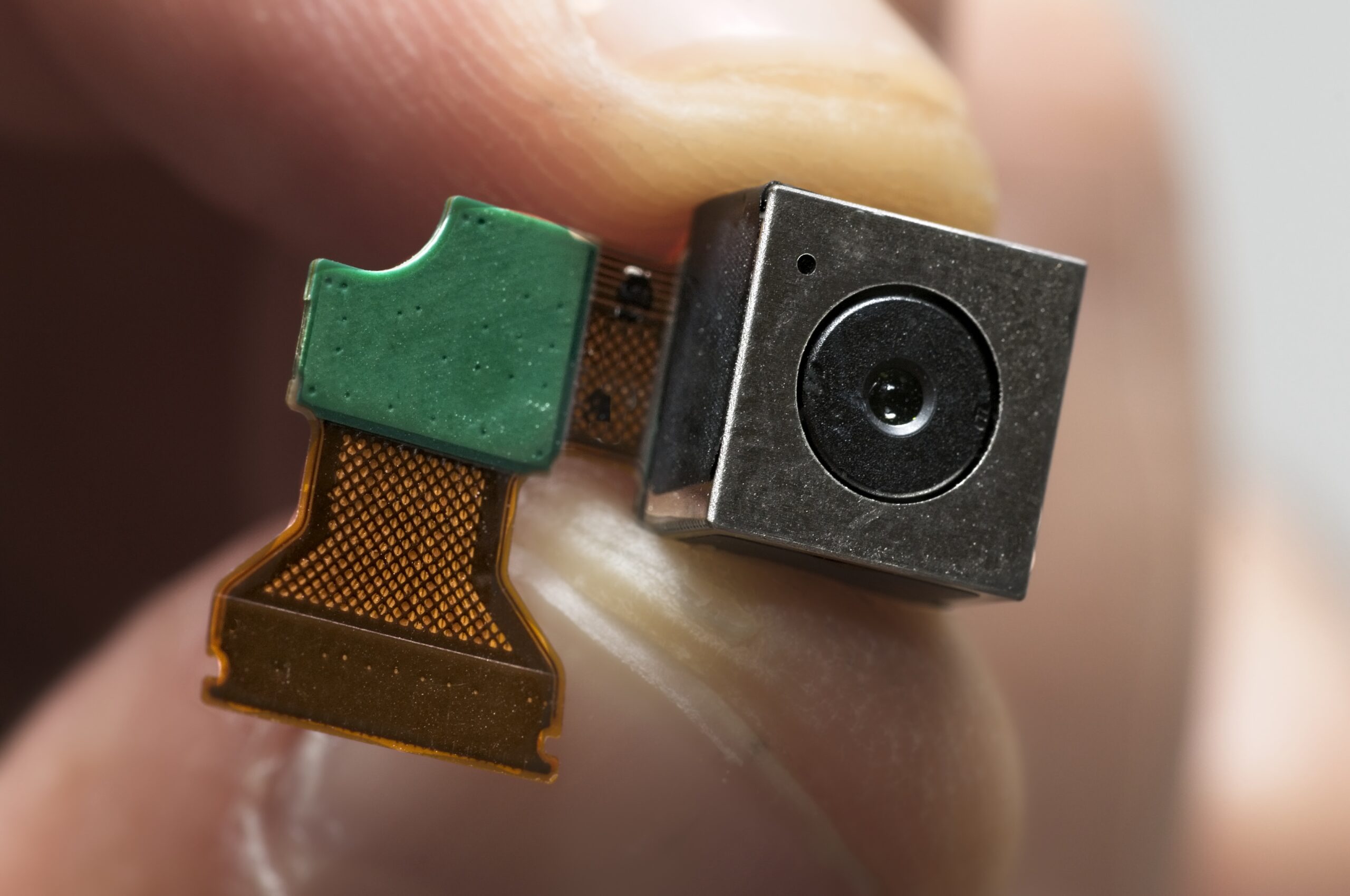
Specific examples of electronic devices commonly utilized for covert eavesdropping encompass pinhole cameras, designed to discreetly capture visual information; 5G recorders and transmitters, capable of intercepting and transmitting data over high-speed networks; GPS trackers for surreptitious location monitoring; hidden microphones embedded in innocuous items like pens or clocks; piggyback keystroke logging devices to clandestinely capture typed information; Raspberry Pi devices employed for covert data collection and manipulation; and phone and wiretaps enabling unauthorized access to communications.
These covert devices leverage advanced technology to capture sensitive information without arousing suspicion, underscoring the necessity for comprehensive security measures. Understanding the intricacies of both the methods employed and the specific electronic devices used is crucial in establishing an effective defense against potential threats in the realm of covert surveillance.
Recent High-Profile TSCM Case
The following is an example of a high-profile case involving a hidden self-contained motion-activated pinhole video camera with a battery power supply and onboard SDHC storage.
This is where NSI Global’s superior methodology and employment of highly sensitive equipment as used by federal governments and intelligence agencies came into play. At NSI Global our government security cleared Technical Surveillance Counter Measures Investigators have been trained and equipped to provide Government Level sweeps.
One example of our superior methodology is the inclusion of High-Resolution Thermal Imaging of all electronic equipment and room surrounds. This revealed any unusual heat signatures to our experienced investigators. This was followed by a thorough teardown inspection of all flagged items.
One item that was identified for further inspection was a common router used in the CEO’s office. On initial inspection, and when subject to a TSCM signal transmission spectrum analysis and network analysis tests, this router came up clean. It was functioning perfectly and showed no signs of tampering.
However, upon further thermal imaging analysis by an experienced investigator we detected an unusual heat signature compared to what is typical for a relatively uncomplicated device. The router was found to have a pinhole high-definition video camera hidden inside its case that was able to record everything being discussed in the office and had a full view of the CEO’s keyboard and computer screen.
Simply put, a standard router would not require any additional internal wiring and certainly should not output heat in several different areas as per the images in this article. The faint outline of wiring and multiple heat sources would be nearly impossible to detect with commercially available thermal cameras.
Upon subsequent physical inspection, a hidden self-contained motion-activated high-definition pinhole video recorder with a 128 GB micro-SD card was discovered.
The router was prepared in such a way that it could easily be swapped after hours with a standard router if the attacker was concerned about an upcoming bug sweep. Additionally, it could be swapped for a second unit containing another camera whilst the footage of the first was being reviewed.
This case highlights the importance of having a robust TSCM strategy of regular sweeps in place. This also serves as a reminder of the potential consequences of failing to adequately protect against eavesdropping and surveillance.
Industries Most at Risk
Industries most at risk include the financial sector, healthcare, and government agencies as well as law firms, technology companies, and manufacturing companies. As a matter of fact, any organization that handles sensitive, strategic, or commercially valuable information can be at risk.
It’s important for all organizations to understand the potentially catastrophic risks they face and to implement robust regular TSCM programs to protect against them.
Safeguarding Your Sensitive Information
Protecting your sensitive information is crucial. This involves implementing strong security measures, educating employees about security risks, and regularly reviewing and updating your security policies. It also involves conducting regular TSCM security audits to identify and address any vulnerabilities.
It’s also important to have a response plan in place in case a breach does occur. This plan should outline the steps to be taken in the event of a breach, including notifying affected parties, investigating the breach, and taking steps to prevent future breaches. Having a response plan in place can help minimize the damage caused by a breach and can help restore trust in your organization.
Conducting Regular Electronic Bug Sweeps
Regular bug sweeps are essential to detect and remove any unauthorised surveillance devices. These sweeps should be conducted by trained professionals using specialised equipment. They should also be conducted on a regular basis to ensure that any new devices are detected quickly.
Bug sweeps can be conducted in a variety of settings, including offices, homes, and vehicles. By conducting regular bug sweeps, you can ensure that your private conversations and sensitive information remain private.
Protecting Executive Offices
Executive offices often contain sensitive information. Conducting a thorough TSCM Inspection of your offices regularly ensures your trade secrets, intellectual property, business strategy, client information, etc. remain safe from the threat of corporate espionage.
It’s important to secure these areas with strong physical and digital security
measures. This can include installing secure doors and windows, using secure
communication lines, and restricting access to these areas.
In addition to physical security measures, it’s also important to implement digital security measures. This can include using encrypted communication channels, installing security software on all devices, and regularly updating all software and hardware. By implementing these measures, you can help ensure that sensitive information remains confidential.
Fortifying the Executive Home Office
As an increasing number of employees opt for private residences as their primary work locations, many leading organizations enlist NSI Global to proactively conduct Technical Surveillance Countermeasures (TSCM) investigations at the residences of executives working from home.
Whether you are a director, employee, or a department head who has identified a potential threat to your organisation’s intellectual property, contact us to ensure the security of your home office.
Securing your home office is crucial for maintaining the confidentiality and integrity of your work. Here are some security recommendations for a work-from-home office:
- Secure Wi-Fi Network: Set up a strong, unique password for your home Wi-Fi
network. Use WPA3 encryption if available for a more secure connection. - VPN (Virtual Private Network): Use a VPN to encrypt your internet connection,
ensuring a secure communication channel between your home office and your
organisation’s network. - Firewall Protection: Enable the firewall on your home router and computer to
prevent unauthorized access. - Device Security: Keep all devices, including computers, routers, and IoT devices,
updated with the latest security patches. Use strong passwords or passphrases for
all devices. - Antivirus Software: Install reputable antivirus and anti-malware software to protect
against malicious software. - Secure Communication: Use secure communication tools and platforms approved
by your organization. Avoid using public Wi-Fi networks for sensitive work-related
communications. - Data Backup: Regularly back up your work-related data to an external hard drive or
a secure cloud service. - Physical Security: Lock your home office when not in use to prevent unauthorised access. Securely store physical documents containing sensitive information.
- Video Conferencing Security: Set up passwords for virtual meetings to prevent
unauthorized access. Be mindful of your surroundings during video calls to avoid
unintentional exposure to sensitive information. - Regular Software Updates: Keep your operating system, applications, and security
software up to date with the latest patches and updates. - Cohabitants: Educate other household members about the importance of security
measures. - Multi-Factor Authentication (MFA): Enable MFA whenever possible to add an extra layer of security to your accounts.
- Secure Document Handling: Store all sensitive documents in a lockable cabinet.
Shred physical documents that are no longer needed. Encrypt sensitive electronic
documents before transferring or storing them. - Work Time Management: Establish clear boundaries between work and personal
time to minimise security risks during non-working hours. - Regular TSCM Security Audits: Regularly conduct TSCM Sweeps to review and
assess your home office security setup in order to identify and address any potential
vulnerabilities and locate any newly hidden devices.
By implementing these and other more comprehensive security recommendations,
NSI Global can help you create a more resilient and secure work-from-home
environment.
Securing Meeting Spaces, Conference Rooms and Boardrooms
Conference rooms, meeting spaces, and boardrooms are often targeted by eavesdroppers. These spaces should be secured with soundproofing, secure communication lines, and regular security sweeps. It’s also important to restrict access to these spaces and to ensure that all attendees are authorized to be there.
In addition to these measures, it’s also important to educate employees about the risks associated with these spaces such as the use of any devices including but certainly not limited to desk phones, keyboards, or tablets that have not been tested and cleared to be free from piggyback devices like keyloggers, pinhole cameras and microphones, or infection by spyware. By taking these steps, you can help ensure that your meetings remain private and secure.
Sensitive Compartmented Information Facilities
For organisations necessitating heightened security protocols for confidential information and discussions, NSI Global offers guidance on establishing a Secure Compartmented Information Facility (SCIF). A SCIF is an enclosed, windowless, and secure space within a building designed for the storage, processing, or discussion of sensitive compartmented information, tailored to the operational needs of the organisation.
While government departments commonly utilize SCIFs, larger private organisations seeking to safeguard sensitive information also find them essential. SCIFs can be either permanent or temporary, and they may be mobile, housed within large vehicles, ships, aircraft, or deployed in the field.
Key characteristics of a SCIF include its status as a secure room or suite of rooms within a facility constructed to elevated security standards, providing physical protection and defense against electronic surveillance from external sources. Unauthorized access is strictly prohibited, and individuals without proper clearance must surrender all electronic devices before entering the SCIF.
Access to the SCIF location is controlled, incorporating alarms, CCTV coverage, secure storage containers, privacy measures against external observation, and routine inspections to ensure the facility is free from bugs or other security risks. Some SCIFs lack electrical cabling, while others monitor all electronic services. Additionally, certain SCIFs are organized with layered security, placing services in the outer ring and restricting them within the SCIF room.
Addressing Vehicle Surveillance
Vehicles can also be a target for surveillance. Consider implementing security measures like regular TSCM vehicle inspections. These measures can help detect and prevent unauthorized surveillance.
It is important to educate drivers about the risks associated with vehicle surveillance. NSI Global’s TSCM Inspectors are well-versed in detecting even the most sophisticated covert devices in all vehicles and other forms of luxury transport.
Additionally, we can detect devices that may be hidden around, or masked by, transmissions of the systems and equipment contained within aircraft and yachts including:
Private Jets
- Instrument Landing Systems (ILS)
- Ground Based Augmentation Systems (GBAS)
- Terminal Area Radars (TAR)
- Automatic Dependent Surveillance Broadcast System (ADS-BS)
- Advanced Surface Movement Guidance and Control Systems (A-SMGCS)
Yachts
- Long Range Open Array Radars
- Wireless CHIRP Radars
- Doppler Collision Avoidance Systems
- Weather Systems Radars
- Radome Systems
- Automatic Identification System
Today’s executives are consistently on the move and there is a need to be constantly connected. Multi-million dollar, and sometimes Multi-Billion dollar decisions cannot wait until you are back in your bug-swept boardroom. Discussions that can make or break a business are now routinely held in Cars, Yachts, and Private Jets. If a competitor can harm you, or profit from tracking you and recording your meetings, your mobile office will be an undeniably attractive target.
Business Risks Associated with Industrial Espionage
Industrial espionage poses several specific business risks, which can have significant consequences for companies. These risks may vary depending on the nature of the industry, the type of information targeted, and the methods used by the perpetrators. Here are some key business risks associated with industrial espionage:
- Loss of Intellectual Property (IP): Industrial espionage often aims to steal valuable intellectual property, such as patents, trade secrets, and proprietary technologies. The unauthorised acquisition of these assets can undermine a company’s competitive advantage, as competitors gain access to innovations and research without investing the necessary time and resources.
- Damaged Reputation: If it becomes known that a company has fallen victim to industrial espionage, its reputation can suffer. Clients, partners, and investors may lose trust in the organisation’s ability to protect sensitive information, leading to a decline in business relationships and market share.
- Financial Loss: The theft of valuable information can result in direct financial losses for a company. Stolen trade secrets or proprietary technologies can be used by competitors, affecting the victim company’s revenue and market position. Additionally, the costs associated with investigating and mitigating the impact of the espionage can be substantial.
- Disruption of Operations: Industrial espionage can disrupt a company’s normal operations, especially if critical information is compromised. This may include disruptions in production, supply chain, or research and development activities, leading to delays and increased costs.
- Legal Consequences: Companies that fall victim to industrial espionage may face legal challenges. This could involve pursuing legal action against the perpetrators or dealing with litigation from stakeholders who suffer harm as a result of the breach. Legal battles can be time-consuming and costly.
- Innovation and Research Setbacks: The theft of research and development data can set a company back in terms of innovation. Competitors gaining access to confidential research can replicate or build upon the stolen information, reducing the victim company’s ability to maintain a technological edge.
- National Security Implications: In cases where industrial espionage involves state-sponsored actors, there may be broader national security implications. The stolen information may have strategic importance, potentially affecting a country’s economic and technological competitiveness.
- Employee Morale and Trust Issues: The discovery of industrial espionage within a company can lead to a breakdown in trust among employees. Suspicion and distrust may arise, impacting the overall morale and productivity of the workforce.
To mitigate these risks, companies must invest in robust ongoing Technical Security Counter Measures Audits, employee training on security best practices, and proactive monitoring for signs of espionage. Working in consultation with NSI Global and developing a comprehensive risk management strategy and collaborating with law enforcement and cybersecurity experts can also be crucial in addressing the challenges posed by industrial espionage.
TSCM as a Risk Management Tool
Technical Surveillance Counter Measures Bug Sweeps (TSCM) can be an effective risk management tool. It is an essential component of an effective NSI Global Security Master Plan that will help you identify and mitigate security risks, protect your assets, and comply with regulatory requirements. By identifying and mitigating risks before they can cause harm, you can prevent financial loss, protect your reputation, and ensure compliance with regulatory requirements.
In addition to preventing harm, TSCM can also provide a return on investment. By preventing security breaches, you can avoid the costs associated with responding to a breach, such as investigation costs, legal fees, and fines. You can also avoid the indirect costs of a breach, such as reputational damage and loss of business.
Enhancing Investor and Customer Confidence
A robust TSCM strategy can enhance investor and customer confidence. It shows that you take security seriously and are committed to protecting your assets and information. This can make your organisation more attractive to investors and can help retain and attract customers.
In addition to enhancing confidence, a robust TSCM strategy can also enhance your organisation’s image. It can show your clients, stakeholders, and the public that you are proactive about security and are committed to protecting your assets and information.
Building a Culture of Security Awareness
Building a culture of security awareness is crucial. This involves educating employees about security risks, implementing strong security policies, and fostering a culture of vigilance. By building a culture of security awareness, you can ensure that all employees understand the importance of security and are committed to protecting your organisation.
Moreover, to build a culture of security awareness, it’s also important to provide ongoing training and support for employees. This can involve regular security briefings, training sessions, and updates. By providing ongoing support, you can ensure that employees have the knowledge and skills they need to protect your organisation.
Implementing Effective Countermeasures
NSI Global provides an extensive array of services dedicated to implementing robust countermeasures, a pivotal element within your TSCM plan. These countermeasures encompass a tailored combination of physical security measures, digital security measures, and routine security audits, precisely crafted to address the distinct threats encountered by your organisation.
In addition to the initial implementation, NSI Global maintains a commitment to ongoing review and updates of these countermeasures. This proactive approach guarantees their sustained effectiveness amidst evolving threats, facilitating the timely identification and mitigation of any emerging risks over time.
Maintaining Ongoing Vigilance
NSI Global takes the lead in providing essential services to maintain ongoing vigilance in safeguarding your security. This encompasses the regular review and updating of your security measures, conducting routine security audits, and staying abreast of emerging threats. Through these practices, NSI Global ensures that your security measures remain effective in the ever-evolving landscape of threats, while also proactively identifying and addressing any new risks that may arise.
In addition to the regular reviews, NSI Global emphasises a proactive stance towards security. This involves actively identifying potential threats, implementing pre-emptive measures to mitigate them before they can cause harm, and being fully prepared to respond swiftly and effectively in the event of a breach.
Staying Informed About Emerging Threats
NSI Global takes the lead in providing crucial services to keep you well-informed about emerging threats, ensuring that you stay one step ahead of potential attackers. This involves staying current with the latest news and developments in the security field, actively participating in relevant security conferences and seminars, and fostering professional connections with other industry experts.
In addition to our commitment to keeping you informed, NSI Global recognises the importance of sharing this knowledge with your team. We facilitate this through regular security briefings, training sessions, and timely updates. By ensuring that your team is well-informed, we empower everyone to stay abreast of the latest threats and equipped with the knowledge to effectively protect against them.
Leveraging Technology for Enhanced Security
Leveraging technology, including AI and machine learning for threat detection, encrypted communication channels, and secure cloud storage for sensitive data, can enhance your security. These technologies, combined with NSI Global’s expertise in technical surveillance countermeasures, provide a more robust and effective defence against threats.
In addition to leveraging technology, NSI Global will help you to understand the risks associated with it. This involves keeping you informed about the latest vulnerabilities and exploits and implementing strong security measures to protect against these risks.
Protecting Your Reputation and Bottom Line
Protecting your reputation and bottom line is crucial. A security breach can damage your reputation and result in financial loss. A robust TSCM strategy can help protect your organisation. It can help prevent security breaches, minimise the damage if a breach does occur, and help restore trust in your organisation.
Moreover, to protecting your reputation and bottom line, a robust TSCM strategy can also enhance your organisation’s image. It can show your clients, stakeholders, and the public that you take security seriously and are committed to protecting your assets and information.
Supply Chain Security and TSCM
Supply chain security is a crucial aspect of TSCM. This involves securing all aspects of the supply chain, from suppliers to transportation, to prevent security breaches. By securing the supply chain, organisations can prevent security breaches, protect their assets and information, and ensure the integrity of their products and services.
In addition to securing the supply chain, organisations must also ensure that they are working with trusted suppliers. This can involve conducting due diligence on suppliers, implementing robust contracts, and regularly reviewing and updating their supplier relationships. By working with trusted suppliers, organisations can ensure that they are receiving high-quality products and services, and can protect their reputation and bottom line.
TSCM in Mergers and Acquisitions
TSCM can play a crucial role in mergers and acquisitions. It can help identify and mitigate security risks, protect sensitive information, and ensure a smooth transition. By implementing robust TSCM measures during mergers and acquisitions, organisations can prevent security breaches, protect their assets and information, and ensure the success of the merger or acquisition.
In addition to implementing TSCM measures, organisations must also ensure that they are conducting due diligence during mergers and acquisitions. This can involve conducting security audits, reviewing contracts and agreements, and ensuring that all parties are aware of their responsibilities. By conducting due diligence, organisations can ensure that they are making informed decisions, and can protect their interests during the merger or acquisition.
Best Practices for Employee Education and Awareness
Educating employees about security risks and best practices is crucial. This can involve regular training sessions, security briefings, and fostering a culture of security awareness. By educating employees, organisations can ensure that they are aware of the risks and know how to protect against them.
In addition to educating employees, organisations must also ensure that they are supporting them. This can involve providing the necessary tools and resources, providing regular feedback and support, and recognizing and rewarding good security practices. By supporting employees, organizations can enhance their security culture, and can ensure that all employees are committed to protecting the organization.
Remember, a robust TSCM strategy is a crucial part of every corporate Security Master Plan we prescribe to our clientele. By understanding the threats, implementing effective countermeasures, and partnering with NSI Global, you can protect your organisation’s sensitive information, reputation, and bottom line.
Complying with Regulatory Requirements
Government agencies must comply with strict regulatory requirements. This includes protecting classified information, addressing foreign intelligence threats, and partnering with law enforcement. By complying with these requirements, government agencies can ensure that they are protecting their assets and information, and are operating within the law.
In addition to complying with regulatory requirements, government agencies must also ensure that they are transparent and accountable. This can involve regularly reporting on their security measures, conducting audits, and being open to scrutiny. By being transparent and accountable, government agencies can build trust with the public and stakeholders.
Protecting Classified Information
Protecting classified information is crucial for government agencies. This involves implementing strong physical and digital security measures, conducting regular security audits, and educating employees about security risks. By protecting classified information, government agencies can prevent security breaches, protect national security, and comply with regulatory requirements.
Additionally, to protect classified information, government agencies must also ensure that they are handling this information responsibly. This can involve implementing strict access controls, ensuring that employees are trained in how to handle classified information, and regularly reviewing and updating their policies and procedures.
Addressing Foreign Intelligence Threats
Foreign intelligence threats are a major concern for government agencies. These agencies must be vigilant in detecting and mitigating these threats. This can involve implementing robust security measures, conducting regular security audits, and partnering with law enforcement and intelligence agencies.
In addition to addressing foreign intelligence threats, government agencies must also be proactive in identifying and mitigating these threats. This can involve staying informed about the latest threats, implementing proactive security measures, and being prepared to respond quickly and effectively if a threat is detected.
Decades at the Forefront of Counterintelligence
Decades at the forefront of counterintelligence have endowed NSI Global with unparalleled capabilities. The success of your TSCM survey and the presentation of indisputable evidence hinge on the ability to uncover even the most sophisticated and latest devices that might otherwise evade detection. Even the most skilled professionals cannot identify the very latest high-spec devices if their equipment is inadequate. Consequently, we have collaborated with manufacturers and made substantial investments to offer industry-leading capabilities, ensuring the detection of even the most advanced covert surveillance devices.
At NSI Global, our extensive international exposure has afforded us numerous opportunities to encounter emerging threats firsthand thus providing us with the knowledge to develop state-of-the-art countermeasures. With advanced technology wielded by our Department of Defence-vetted specialists, we possess the capacity to furnish evidence that could make or break your case, as well as provide recommendations to address identified vulnerabilities.
Detailed Insights from The TSCM Authority
A comprehensive report will be furnished, detailing all findings, whether they pertain to discovered covert devices or identified vulnerabilities. Additionally, we will offer appropriate recommendations to effectively mitigate these technical surveillance risks in the future. If necessary, these detailed reports can be meticulously prepared to meet legal standards for submission as evidence in a court of law.
For over two decades, we have adeptly addressed the requirements of Courts, Commissions, and Inquiries, providing concise evidence and expert witness testimony. Our Litigation Support Services extend across the entire litigation process, encompassing initial case assessment, the utilisation of analytics, assisted review technologies, and culminating in trial proceedings.
The expertise gained through the aforementioned experiences positions NSI Global as a highly sought-after authority when your privacy is compromised, and you seek the counsel of an advisor with a proven track record of delivering results.
Partnering for Comprehensive Protection
Partnering with NSI Global can provide comprehensive protection for your organisation. They can help you develop a customised TSCM plan, implement effective countermeasures, and maintain ongoing vigilance. They can also provide training for your employees, helping them understand the risks and how to protect against them.
In addition to providing comprehensive protection, partnering with NSI Global can also provide peace of mind. Knowing that you have a team of experts working to protect your organisation can help you focus on your core business activities. It can also enhance your reputation, showing your clients and stakeholders that you take security seriously.
If you have any questions about this article or would like to enquire about our range of other services, please call 1300 000 NSI (674).