By: Claude Khoury
Both WhatsApp and Israeli software developer NSO Group have confirmed that an exploit in WhatsApp voice calling allowed attackers to install NSO’s Pegasus spyware on to both Android and iOS devices. This covert tool can infect a device even if the user doesn’t answer, and the malicious calls would regularly disappear from logs. Pegasus hijacks the camera and mic and records location and message info.
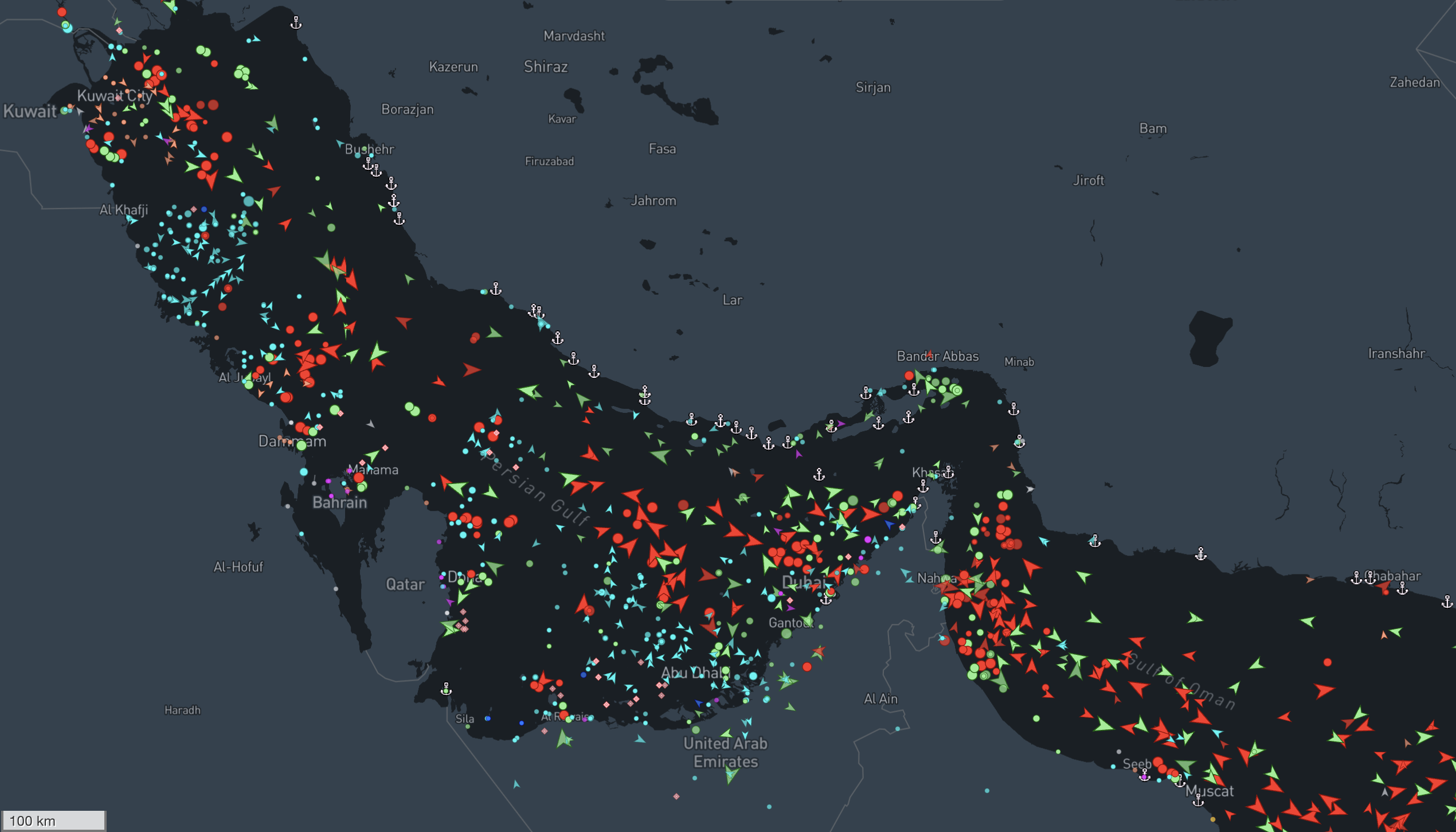
At this stage, there are suspicions that it may be a Middle Eastern country trying to monitor criticism of its human rights practices. On May 12th 2019 there was an attempt made to compromise the mobile phone of a UK-based human rights lawyer who represented a Saudi dissident in Canada and helped sue NSO for allegedly sharing in the liability of actions perpetrated by its users. NSO sells its software to Middle Eastern intelligence agencies. Allegedly, human rights activists in the Middle East have previously received text messages attempting to install Pegasus on their devices.
WhatsApp has now alerted the US Justice Department and human rights groups. WhatsApp stated the incident had “all the hallmarks” of a private company that works with governments to propagate spyware. NSO rejected the idea that it was involved in any way. “Under no circumstances would NSO be involved in the operating or identifying of targets of its technology,” the company said. NSO has further stated that it screens all customers and investigates abuses, including the aforementioned attack on the UK lawyer.
The flaw should have been patched as of the release of this article. WhatsApp delivered a server-side fix on May 10th 2019 and has released patched versions of its apps on May 13th 2019. However, that still does not address concerns that companies like NSO, Hacking Team, and others, have allegedly sold spyware to several countries with a history of cracking down on dissidents. There are efforts to impose a restriction on these relationships, such as an upcoming challenge to NSO Group’s export abilities on May 15th 2019. Moving forward, it may be difficult to prevent spyware campaigns like this if this effort is unsuccessful.