In today’s digital age, the internet has become an integral part of our lives. While it offers numerous benefits, it also exposes individuals to potential online threats. Attackers, driven by various motives, exploit vulnerabilities to compromise personal information, privacy, and security. This article aims to explore the different attack vectors that malicious actors might employ to investigate individuals online. By understanding these vectors, we can better protect ourselves from potential harm.
- Social Engineering: Through clever manipulation and deception, attackers exploit human psychology to gather sensitive information from unsuspecting individuals. This can involve phishing emails, phone scams, or impersonating trusted entities to trick victims into divulging personal data.
- Password Attacks: Attackers leverage techniques such as brute-force attacks, dictionary attacks, or using stolen credentials to gain unauthorized access to personal accounts. Weak or reused passwords increase the risk of successful password attacks.
- Malware and Exploits: Exploiting software vulnerabilities or tricking individuals into downloading infected files are common techniques used by attackers. Malicious software, such as viruses, worms, or Trojans, can infect devices and provide attackers with unauthorized access.
- Online Identity Theft: Attackers will hack databases to gain access to personal information, such as social security numbers, credit card details, or login credentials, to assume someone else’s identity. This stolen information can be misused for financial gain or other malicious purposes.
- Phishing and Spear Phishing: Phishing involves sending fraudulent emails, messages, or websites that mimic legitimate ones to deceive individuals into revealing sensitive information. Spear phishing is a targeted form of phishing where attackers personalize their messages to increase the chances of success.
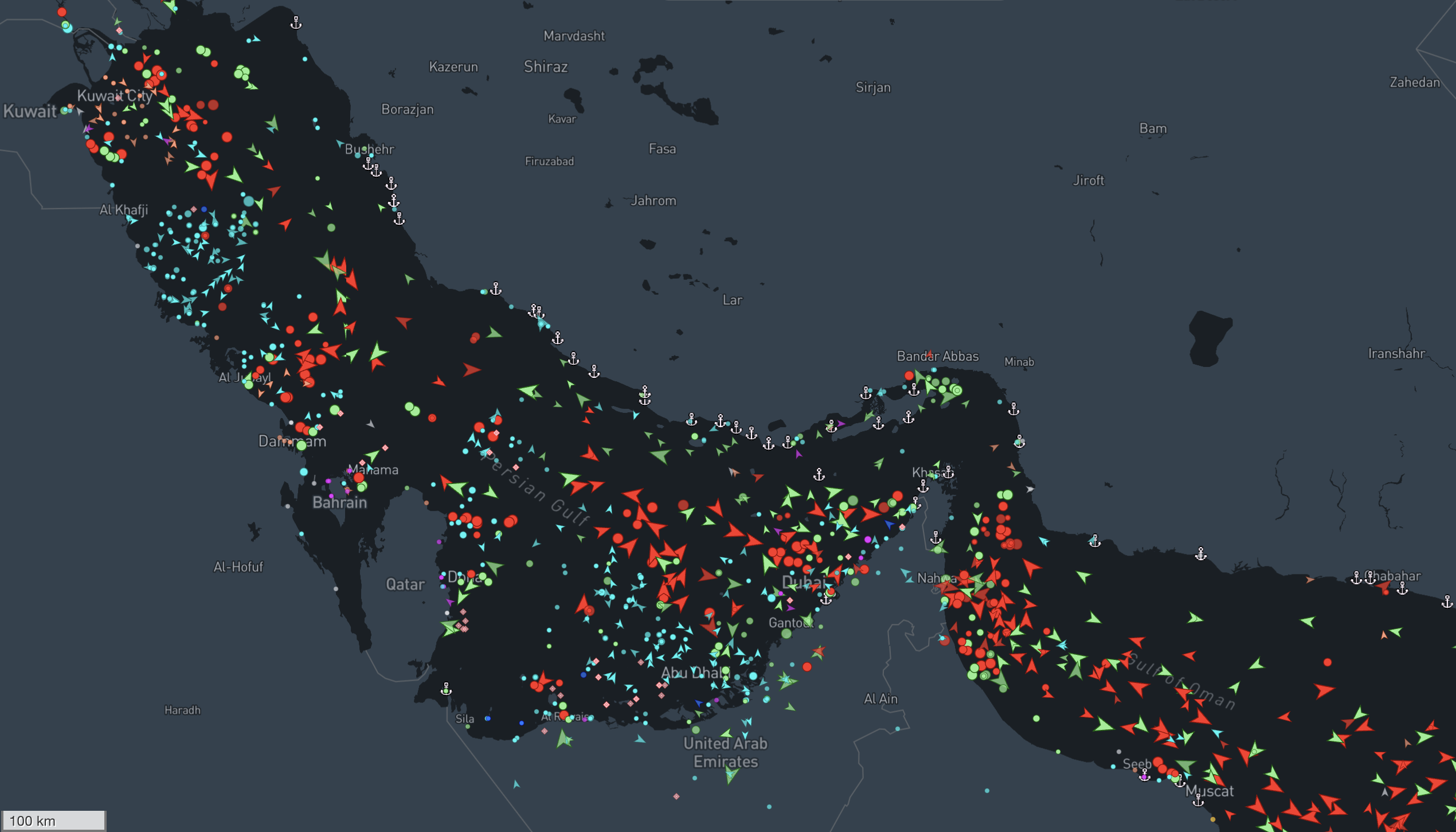
- Social Media Exploitation: Publicly available information on social media platforms can be exploited by attackers. Personal details, location check-ins, or posts revealing travel plans can help attackers gather information for targeted attacks or physical threats.
- Public Wi-Fi and Network Sniffing: Unsecured public Wi-Fi networks pose risks, as attackers can intercept network traffic and capture sensitive information. This technique, known as network sniffing, can compromise personal data transmitted over these networks.
- Online Tracking and Profiling: Attackers may employ various tracking techniques, such as cookies or browser fingerprinting, to monitor an individual’s online activities. This data can be used for targeted advertising, identity profiling, or other intrusive purposes.
- Online Scams and Fraud: Attackers employ scams such as advance fee fraud, lottery scams, or fake investment opportunities to deceive individuals into providing money or sensitive information. Awareness and scepticism are crucial in avoiding falling victim to such scams.
- IoT Vulnerabilities: As the Internet of Things (IoT) expands, connected devices become potential targets. Attackers can exploit vulnerabilities in smart home devices, wearables, or even connected cars to gain unauthorized access to personal information or compromise safety.
NSI Global can assist your organisation with Offensive Cyber Security Services in Australia, specialised penetration testing such as red and purple team testing, and threat intelligence reporting. By leveraging NSI Global’s expertise and solutions, our clientele can fortify their digital defenses and protect their business and personal information from cyber threats. Stay vigilant, stay secure, and let NSI Global be your trusted partner in the ever-evolving landscape of cybersecurity. For a confidential discussion regarding your risk profile, contact NSI Global today.