An extremely potent malware, delivered in a way that’s immune to most cyber security measures, was discovered infecting high-profile Chinese individuals.
Cybersecurity researchers from Kaspersky have discovered malware they call WinDealer, distributed and used by a Chinese Advanced Persistent Threat (APT) actor called LuoYu. WinDealer, the researchers say, can collect “an impressive amount” of information. It can view and download any files stored on the device, as well as run a keyword search on all the documents.
WinDealer is demonstrating “seemingly impossible network behaviours” via infrastructure that is “nothing short of extraordinary” according to a striking new report by security researchers at Kaspersky Lab — who believe the threat group has the unusual and highly sophisticated ability to conduct hugely powerful “man-on-the-side” (MOTS) attacks like those of the NSA and GCHQ’s “Quantum Insert” project, which were revealed in Edward Snowden’s 2013 leaks.
“We speculate that the attackers may have the following capabilities: Intercepting all network traffic, which allows them to receive backdoor responses to random IP addresses without having to deploy actual C2 servers. Injecting arbitrary TCP and UDP packets on the network, a capability through which they can send orders to WinDealer. Full control over the DNS, meaning they can provide responses for non-existent domains. Either QUANTUMINSERT capabilities or the ability to modify the contents of HTTP packets on the fly, thanks to which they can achieve remote, zero-click malware installation by abusing auto-update mechanisms.” Kaspersky said
Russia’s Kaspersky Lab has been tracking LuoYu alongside Taiwanese threat hunters TeamT5 and security researchers at Japan’s ITOCHU Corporation and presented on the group’s TTPs in January.
The APT has been active since 2014 and initially focussed on Chinese dissidents as well as foreign embassies in China.
It has since expanded its scope to neighbouring countries and IT companies the three organisations said this year.
Kaspersky added this week that its telemetry suggested “occasional infections in other countries such as Germany, Austria, the United States, Czech Republic, Russia and India” and noted that “in recent months, LuoYu has started to widen its scope to companies and users in East Asia and their branches located in China…”
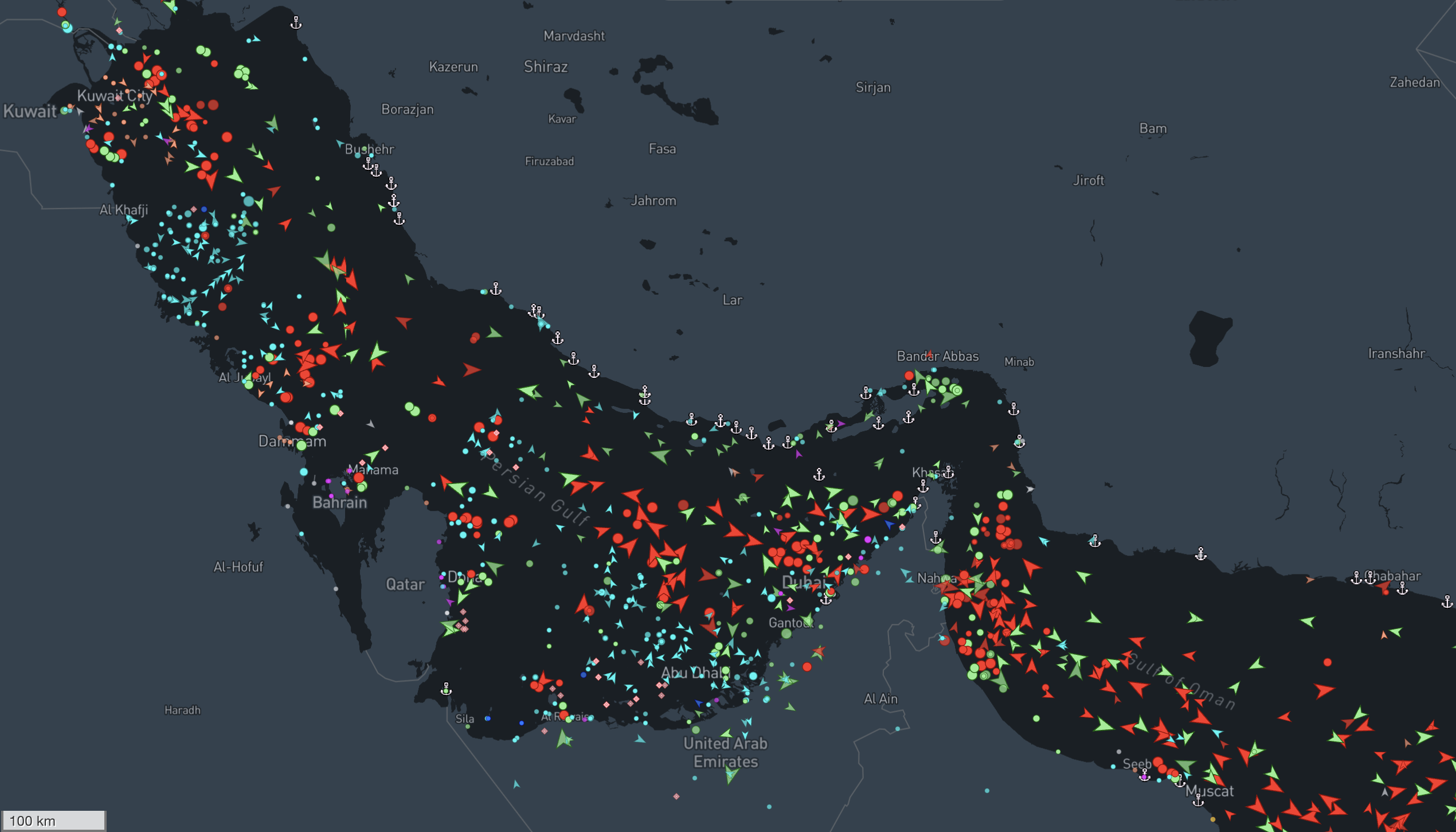
A WinDealer sample reviewed by Kaspersky does not contain a hard-coded Command and Control (C2) server but instead “relies on a complex IP generation algorithm to determine which machine to contact… the end result is that the IP address is selected at random from one of these two ranges:113.62.0.0/15 [and] 111.120.0.0/14″ Kaspersky said. Once the IP address has been selected, communications take place either over UDP port 6999 or TCP port 55556:
“In an even weirder twist… an additional WinDealer sample communicates with the hard-coded URL http://www[.]microsoftcom/status/getsign.asp. This domain is obviously invalid and cannot resolve to anything in normal circumstances – yet the malware expects a response in a predetermined format.”
“It is very hard to believe that an attacker would be able to control the 48,000 IP addresses of the aforementioned IP ranges, or even a significant portion of them” Kaspersky’s threat hunting team said in a June 2 blog. “The only way to explain these seemingly impossible network behaviours is by assuming the existence of a man-on-the-side attacker who is able to intercept all network traffic and even modify it if needed.”
More broadly, the WinDealer malware suite is multifaceted and capable of a range of offensive capabilities, Kaspersky said, including file and file system manipulation: reading, writing and deleting files, listing directories, obtaining disk information; information gathering as well as “collecting hardware details, network configuration and/or keyboard layout, listing running processes, installed applications and configuration files of popular messaging applications (Skype, QQ, WeChat and Wangwang); download and upload of arbitrary files; arbitrary command execution; system-wide search across text files and Microsoft Word documents; screenshot capture; network discovery via ping scan and backdoor maintenance: set up or remove persistence (via the registry’s RUN key); more.”
The Quantum Insert man-on-the-side attacks revealed in 2013 that it appears western intelligence agencies had been deploying since 2005 involved deploying what Wired describes as “fast-acting servers relatively near a target’s machine that are capable of intercepting browser traffic swiftly in order to deliver a malicious web page to the target’s machine before the legitimate web page can arrive… as well as special high-speed servers known as “shooters,” placed at key points around the internet”.
Kaspersky’s own description of MOTS attacks this week said: “The attacker sees a request for a specific resource on the network, it tries to reply to the target faster than the legitimate server. If the attacker wins the “race”, the target machine will use the attacker-supplied data instead of the normal data.
This is consistent with the scenario described earlier in this article, where the target receives an infected executable instead of the normal one. Automatic updaters are prime targets for such attacks as they perform frequent requests – it doesn’t matter if the attackers don’t win most races, as they can try again until they succeed, guaranteeing that they will infect their targets eventually.
This class of attack is particularly devastating because there is nothing users can do to protect themselves, apart from routing traffic through another network. This can be done with the use of a VPN, but these may be illegal depending on the jurisdiction and would typically not be available to Chinese-speaking targets.”