In today’s highly competitive business landscape, the threat of corporate espionage looms large. Competitors, disgruntled employees, and even state-sponsored actors may attempt to gain unauthorised access to your company’s confidential information, trade secrets, and intellectual property. To ensure the security and integrity of your organisation, it is imperative to implement robust measures that effectively detect and mitigate illegal electronic surveillance devices. In this article, we will explore the realm of technical surveillance countermeasures (TSCM) and delve into the crucial role played by TSCM services in safeguarding businesses against electronic eavesdropping.
Understanding the Need for Technical Surveillance Countermeasures
The High Stakes of Corporate Espionage
The consequences of falling victim to corporate espionage can be devastating for businesses. Intellectual property theft can result in significant financial losses, damage to reputation, and erosion of competitive advantage. Moreover, the breach of sensitive customer data can lead to legal and regulatory repercussions, as well as the loss of customer trust. It is therefore paramount for organisations to proactively protect themselves against these threats.
The Role of Technical Surveillance Countermeasures
Technical Surveillance Countermeasures, commonly referred to as TSCM, encompass a range of proactive measures designed to detect and mitigate electronic surveillance devices. TSCM involves the systematic inspection and analysis of physical spaces, communication networks, and electronic devices to identify and neutralise any unauthorised illegal monitoring devices.
Electronic Bug Detection: Unmasking the Threats
Understanding Electronic Bugs
Electronic bugs, also known as surveillance devices or listening devices, are covert devices that are surreptitiously placed in target areas to capture sensitive information without the knowledge or consent of those being monitored. These devices can come in various forms, including wireless transmitters, hidden microphones, or even modified everyday objects.
Detecting Electronic Bugs
The process of detecting electronic bugs requires specialised expertise and advanced equipment. TSCM professionals employ a variety of techniques and tools to sweep the target areas for hidden surveillance devices. These can include radio frequency (RF) spectrum analysers, non-linear junction detectors, thermal imaging cameras, and sophisticated audio monitoring equipment.
Technical Surveillance Countermeasures (TSCM) Services: A Comprehensive Solution
The TSCM Process: A Step-by-Step Overview
- Consultation and Risk Assessment: TSCM service providers begin by understanding the unique needs and risks of the client’s business. This involves conducting comprehensive consultations, assessing vulnerabilities, and defining the scope of the TSCM operation.
- Physical Inspection and Electronic Sweeps: TSCM professionals meticulously inspect physical spaces, including offices, meeting rooms, and executive vehicles, for any signs of covert surveillance devices. Electronic sweeps are conducted to detect RF emissions, hidden microphones, and other electronic bugs.
- Network Analysis and Vulnerability Assessment: TSCM experts analyse the organisation’s communication networks and IT infrastructure to identify potential vulnerabilities that could be exploited for surveillance purposes. This includes assessing the integrity of wireless networks, email systems, and other communication channels.
- Countermeasures Implementation: Based on the findings of the TSCM assessment, appropriate countermeasures are implemented to neutralise detected threats and enhance the overall security posture of the organisation. This may involve the physical fortification of the premises, network hardening, and employee education and awareness programs.
- Post-Sweep Analysis and Reporting: After completing the TSCM operation, a detailed report is provided to the client, highlighting the findings, recommended countermeasures, and ongoing security best practices. This ensures that the organisation remains vigilant and can address future threats effectively.
Benefits of Professional TSCM Services
By engaging professional TSCM services, businesses can reap several key benefits:
- Proactive Threat Detection: TSCM professionals are trained to identify and neutralise surveillance threats before they can cause harm. Their expertise and state-of-the-art equipment enable them to detect even the most sophisticated electronic bugs, giving organisations a crucial advantage in staying one step ahead of potential espionage attempts.
- Comprehensive Security Assessments: TSCM services encompass not only the detection of electronic surveillance devices but also a comprehensive assessment of physical spaces, communication networks, and IT systems. This holistic approach ensures that all potential vulnerabilities are addressed, providing organisations with robust protection against multiple threat vectors.
- Confidentiality and Privacy Preservation: TSCM operations are conducted with utmost discretion and respect for client confidentiality. Professional TSCM providers adhere to strict ethical standards and take measures to safeguard sensitive information throughout the engagement.
- Legal and Regulatory Compliance: By employing TSCM services, organisations demonstrate their commitment to maintaining compliance with relevant privacy laws and regulations. This can help mitigate legal risks and potential liabilities associated with data breaches and unauthorised surveillance.
- Peace of Mind: Perhaps most importantly, engaging professional TSCM services gives business owners, executives, and stakeholders peace of mind. Knowing that comprehensive measures are in place to protect sensitive information fosters a secure and productive working environment, allowing organisations to focus on their core objectives without the constant fear of espionage threats.
Live TSCM Meeting Monitoring: Guarding Your Confidential Discussions
The Vulnerability of Live Meetings
Live meetings, whether internal strategy sessions or confidential negotiations with external parties, can be particularly susceptible to eavesdropping and surveillance. The potential consequences of unauthorised access to such discussions can be severe, ranging from the compromise of sensitive business strategies to the leakage of confidential merger and acquisition plans.
Implementing Live TSCM Meeting Monitoring
To mitigate the risks associated with live meetings, organisations can employ live TSCM meeting monitoring solutions. These solutions involve the deployment of specialised equipment and technologies that detect and neutralise potential eavesdropping devices, ensuring that discussions remain private and secure.
Advanced Technologies for Live Meeting Monitoring
Live meeting monitoring solutions leverage cutting-edge technologies to detect and thwart potential surveillance attempts. These can include:
- Acoustic Monitoring Systems: Sophisticated audio monitoring systems can analyse the ambient sound patterns in a meeting room and identify anomalies that could indicate the presence of hidden microphones or other covert recording devices.
- Radio Frequency Monitoring: RF monitoring equipment can detect unauthorised RF emissions, wireless transmitters, and other devices that operate in the radio frequency spectrum. By scanning for RF signals, TSCM professionals can identify and neutralise potential eavesdropping threats.
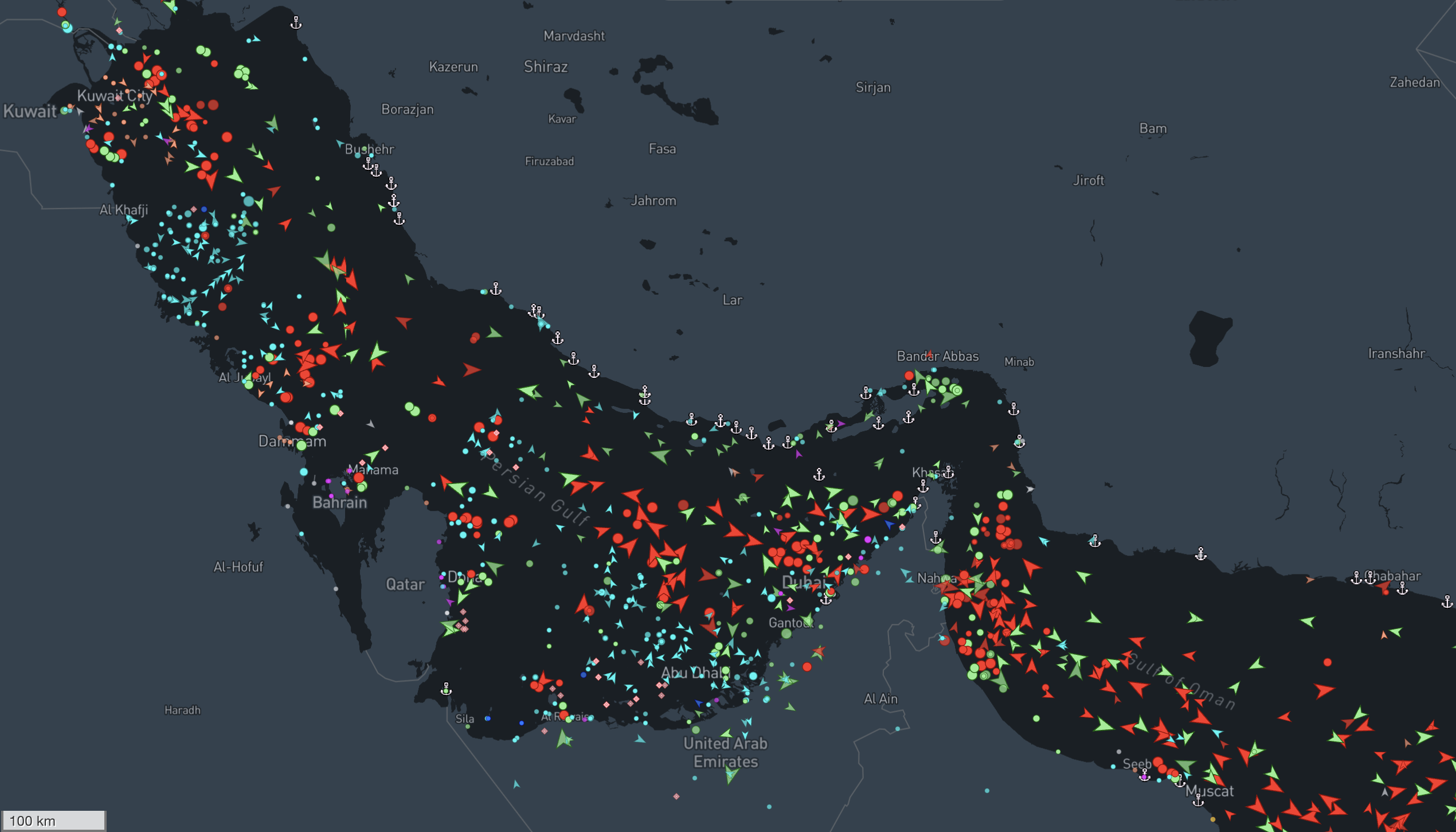
- Signal Analysis and Triangulation Advanced signal analysis software can identify and locate hidden covert surveillance devices. Working off of a loaded floorplan of the meeting venue we can monitor rogue signals entering and leaving the premises in real-time, ensuring the confidentiality of live meetings.
The NSI Global Advantage: Protecting Your Business with TSCM Services
When it comes to securing your business against corporate espionage and electronic eavesdropping, NSI Global stands out as a trusted and experienced partner. With a wealth of expertise in technical surveillance countermeasures, NSI Global offers comprehensive TSCM services tailored to the unique needs of each client.
By engaging NSI Global’s TSCM electronic bug detection services, you gain access to:
- A team of highly skilled and certified TSCM professionals with extensive experience in mitigating electronic surveillance threats.
- State-of-the-art detection equipment and technologies that enable precise and effective identification of hidden bugs and surveillance devices.
- Thorough risk assessments and comprehensive security audits that encompass physical spaces, communication networks, and IT systems.
- Customised countermeasures and security solutions designed to address identified vulnerabilities and protect your organisation’s sensitive information.
- Discreet and confidential operations that prioritise the privacy and integrity of your business discussions and operations.
Don’t leave the security of your business to chance. Safeguard your organisation’s most valuable assets with NSI Global’s trusted TSCM security sweep services. Contact us today to learn more about how we can help you stay one step ahead of the ever-evolving threats of corporate espionage.
Frequently Asked Questions (FAQs)
- What are technical surveillance countermeasures (TSCM)? Technical surveillance countermeasures, or TSCM, refers to the process of detecting and mitigating electronic surveillance threats. It involves the systematic inspection and analysis of physical spaces, communication networks, and electronic devices to identify and neutralise unauthorised monitoring devices.
- Why is TSCM important for businesses? TSCM is crucial for businesses because it helps protect against the risks of corporate espionage, information theft, and unauthorised surveillance. By proactively implementing TSCM measures, organisations can ensure the security and integrity of their sensitive information, maintain competitive advantage, and safeguard customer trust.
- What are electronic bugs? Electronic bugs are covert surveillance devices that are surreptitiously placed to capture sensitive information without the knowledge or consent of those being monitored. These bugs can take various forms, including hidden microphones, wireless transmitters, or modified everyday objects.
- How do TSCM services detect electronic bugs? TSCM professionals use specialised equipment and techniques to detect electronic bugs and will never use bug detection equipment or bug detectors easily found online. This specialised equipment includes radio frequency (RF) spectrum analysers, non-linear junction detectors, thermal imaging cameras, and audio monitoring equipment. These tools help identify RF emissions, hidden microphones, and other electronic surveillance devices.
- How often should TSCM assessments be conducted? The frequency of TSCM assessments depends on various factors, such as the nature of the business, level of sensitivity of the information being protected, and the evolving threat landscape. It is recommended to conduct regular TSCM assessments, especially during significant events like mergers, acquisitions, or executive transitions, to ensure ongoing security.
As the threat of corporate espionage continues to grow in our interconnected world, businesses must take proactive measures to protect their sensitive information and maintain a competitive edge. Technical surveillance countermeasures (TSCM) services provide organisations with the necessary expertise, tools, and strategies to detect and mitigate electronic surveillance threats effectively.
By engaging professional TSCM services, such as those provided by NSI Global, businesses can proactively safeguard their confidential discussions, protect their intellectual property, and ensure compliance with privacy laws and regulations. Don’t let your valuable information fall into the wrong hands—prioritise TSCM as a critical component of your organisation’s security strategy. Contact NSI Global today for a confidential consultation regarding your counter-espionage requirements.