By: Navid Sobbi
Research from Newcastle University shows that PINs and passwords can be discovered by apps that hijack your mobile device’s onboard sensors. The cyber experts at Newcastle University in the United Kingdom have revealed how easy it is for malicious websites and apps to spy on us using the sensors in our mobile phones. Analysing the movement of a mobile device as information is being typed into it has shown that it is possible to crack a four-digit PIN code with 70% accuracy on the first guess. It rises to 100% accuracy by the fifth guess, all by using the data collected via the phone’s numerous internal sensors.
In spite of the threat, the research shows that people are unaware of the risks and most have little idea what the majority of the many different sensors available on current smartphones do. And while all the major players in the industry are aware of the problem, no-one has yet been able to find a solution.
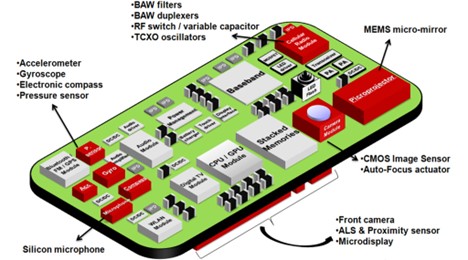
Most smartphones, tablets, and other wearables are now equipped with a multitude of sensors, from the well-known GPS, camera and microphone to instruments such as the gyroscope, rotation sensors and accelerometer. But because mobile apps and websites don’t need to ask permission to access most of them, malicious programs can covertly ‘listen in’ on your sensor data and use it to discover a wide range of sensitive information about you such as phone call timing, physical activities and even your touch actions, PINs and passwords. And worse still, in some cases, unless you close them down completely, they can even spy on you when your phone is locked
Sensors are now commonplace in smart devices and are largely responsible for the boom in mobile gaming and health and fitness apps, and soon in all devices in the Internet of Things (IoT). The data provided by them combined with the growing computational ability of mobile phones and tablets has transformed the way we use them. In total, the research team identified 25 different sensors which now come as standard on most smart devices and are used to give different information about the device and its user. Only a small number of these – such as the camera and GPS – ask the user’s permission to access the device.
Despite the very real risks, when we asked people which sensors they were most concerned about we found a direct correlation between perceived risk and understanding. So people were far more concerned about the camera and GPS than they were about the silent sensors.
Whenever a user touches their screen – either by clicking, scrolling, holding and tapping – a unique orientation and motion trace is induced.
How can you protect yourself?
Below are some tips you should follow to protect yourself and your data:
- Tip 1: Make it a habit to change your PIN codes and passwords regularly so malicious apps and websites don’t recognise patterns.
- Tip 2: Always make sure your phone’s operating system and apps are up to date.
- Tip 3: Close all background apps when you are not using them and remove apps you no longer use as these may collect data also.
- Tip 4: Disable apps that collect information such as your location when you are not using them. Only allow this when you are using the app.
- Tip 5: Only install apps from approved app stores and ensure the apps have been verified by the App Store or Play Store.
- Tip 6: Review all permissions set for each app on your phone.
- Tip 7: When installing apps, carefully look at the permissions requested. For example, if a calculator app is requesting permission of your location and microphone without a valid reason as to why it needs this, it is not recommended to install it.
Our expert information, operation and cyber risk advisors can help you with detecting and advice on mobile device security. For other advice on Digital Forensic Investigations and Counter Intelligence Services, please do not hesitate to contact NSI Global Counter Intelligence for a confidential consultation.