The levels of industrial and economic espionage have been on the rise in recent years with the advent of readily available equipment that can be purchased online. Devices such as electronic bugs, listening devices, hidden cameras, Cellular interception, Bluetooth interception, laser microphones, burst transmitters, and other similar eavesdropping devices are all easily available over the internet to anyone with a credit card. As a result, there is now a greater threat present than ever before, especially for businesses. The risk for businesses is that their sensitive information such as proprietary product specifications or formulas, business plans, and client data can be exploited. Typically, industrial spies are seeking any data they can exploit to gain an advantage, whether that’s selling it to third parties or using it for a competitive advantage.
Technical Surveillance Counter Measures (TSCM) is a service provided to detect the presence of technical surveillance devices and hazards and to identify technical security weaknesses that could aid in the conduct of a technical penetration of the surveyed facility. A TSCM survey will provide a professional evaluation of the facility’s technical security posture and normally will consist of a thorough visual, electronic, and physical examination in and about the surveyed facility.
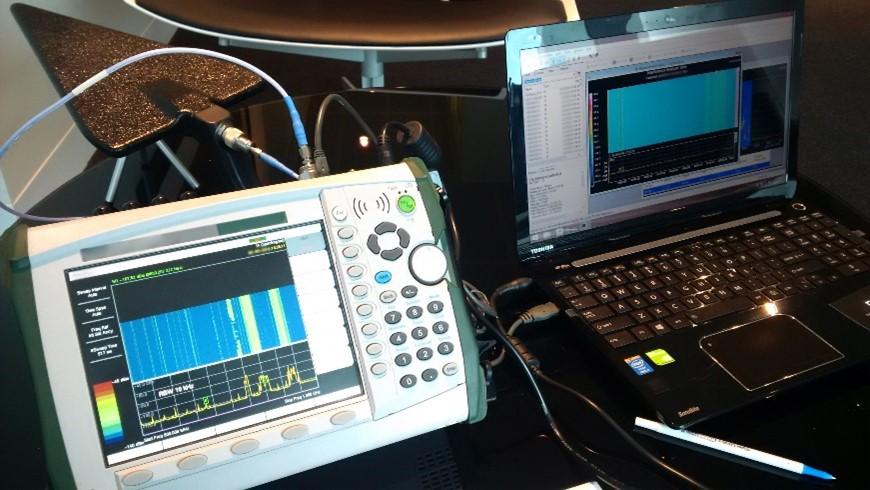
Live monitor of a corporate clients board meeting.
In the TSCM industry, most basic sweeps provided by other service providers will only scan for transmissions from covert devices and electronic signatures. What happens when the bug is not a transmitter and its electronic signature is masked by hiding it within other electronics? Companies only scanning in this way will not be able to detect a recording device installed within other electronics. The benefits of a full, comprehensive TSCM Bug Sweep and security audit are immeasurable if your business has any sensitive information that can be stolen.
The benefit of commissioning an expert TSCM provider to conduct a sweep is that they will analyse the entire working environment including the premises, the staff, your practices, your technology, and external threats. After completing a full technical threat assessment, a unique security package is then designed for the business catered to the specific environment and circumstances. In conducting work in such a manner, it uncovers all potential vulnerabilities that could be exploited to steal information.
The benefits of conducting Security Audits and TSCM Sweeps far outweigh the potential consequences of having data leaked and/or stolen. It is a simple cost/benefit analysis that all businesses should endeavour to fully consider in the review of their annual operations. The cost of risk mitigation mechanisms, such as an annual TSCM sweep and audit, will be a fraction of the cost the business could endure if sensitive information was indeed compromised. Most companies will spend more per annum employing one security guard to greet customers then they would protecting against industrial espionage. Companies have come to realise the reasonable costs required to perform regular TSCM Bug Sweeps to protect company assets are minuscule when compared to the potential damages, both economic and reputational, that could arise from inadequate security protocols.




